Cyber Security
The study programme Cyber Security equips the graduates with in-depth knowledge of methods and techniques of security and protection of organizations, their information systems and employees against cyber threats. The students acquire the understanding of the impact of cyber risks on business operations, the knowledge of the right requirements and related legislation, as well as the methods of assessing or auditing cyber security.
Virtual real-time attendance at lectures
Optional live or virtual real-time attendance at tutorials
Enrolment into the 1st year
The following candidates may enrol in the first year of the Master’s study programme Cyber Security:
- Those who have completed a first-cycle study programme in the fields of informatics or computer science (Klasius-P-16: 06). The competent faculty authority does not prescribe additional study obligations based on the application for enrolment.
- Those who have completed a first-cycle study programme in other fields of study. Based on the application for enrolment, the competent FIŠ authority prescribes additional study obligations to the candidate in the range of 10 ECTS.
For graduates of higher professional study programmes adopted before 11 June 2004, the provisions for graduates of first-cycle study programmes apply mutatis mutandis.
Enrolment into the 2nd year
The following candidates may enrol directly into the second year of the Master’s study programme Cyber Security:
- Those who have completed a study programme for obtaining a university education or specialization, adopted before 11 June 2004, in the fields of computer science and informatics (Klasius-P-16: 06). Upon enrolment, the candidate is recognized with 60 ECTS.
Candidates who have completed equivalent education abroad may also enrol in the first or second year. At the request of the applicant, FIS determines the equivalence of the education acquired abroad within the procedure of education recognition.
Applications for transitions between other programmes, specialist study programmes, scientific master’s study programmes and second-cycle master’s studies are considered individually by the competent FIS authority.
To advance from the first to the second year, the student must acquire at least 45 ECTS from the first year. The faculty may allow the student to advance to a higher year, even if the required conditions are not met, in the following circumstances: maternity, prolonged illness, exceptional family or social circumstances, participation in top cultural, sports or professional events. A student who does not meet the conditions for enrolling in a higher year may repeat a year once during their studies or change their study programme or course due to non-fulfilment of obligations in the previous study programme or course. It is not possible to repeat the second year because an additional year (absolventski staž) is intended for fulfilling the missing obligations.
The condition for the completion of studies is the successful completion of all study obligations prescribed by the programme in the amount of 120 ECTS. A student who enrols directly in the second year, after completing a university education or specialization according to a programme adopted before 11.06.2004, must pass all prescribed differential exams and full-time study obligations of the second year. The study ends with the preparation and oral defence of the master’s thesis.
Students of the master’s programme Cyber Security obtain the following competences:
- Understanding the importance of cyber security.
- Ability to identify cybersecurity threats and provision of protective countermeasures based on the security threats assessment.
- Ability to collect, select, analyze information and capability to interpret it in order to provide holistic problem resolutions, as well as challenges and incidents in the field of cybersecurity.
- In-depth understanding of the functioning of organizational information systems, components and networks.
- Ability to use various software solutions to ensure, manage, monitor and evaluate cyber security.
- Knowledge of established methodological approaches for managing the security of modern information systems and networks.
- Ability to search for sources and obtain data for cybersecurity management needs.
- The ability of business communication, teamwork and the use of information technologies for the purpose of ensuring cyber security.
- Ability to develop an organization’s information security policies and management systems.
- The ability to flexibly apply acquired knowledge about cyber security in practice.
- Striving for quality of professional work through autonomy, (self-) criticism, (self-) reflection and (self-) evaluation of the professional work
- Knowledge of legal and ethical aspects of data and information protection.
Students of the master’s programme Cyber Security will also obtain course-specific competences, which are listed in the individual curricula of the programme’s curriculum.
Curriculum - Cyber Security (MA)
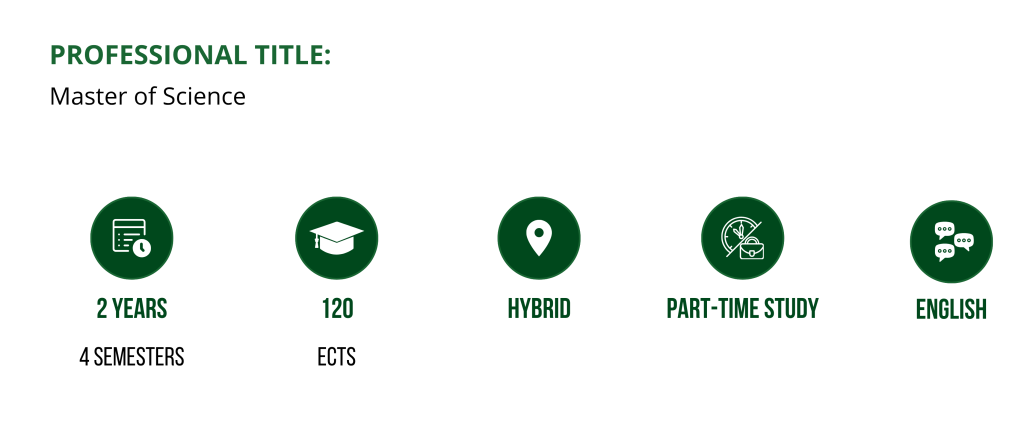
The programme lasts 2 years and is divided into 4 semesters. It ends with the preparation of a master’s thesis. Consequently, in the third semester, the student selects a mentor for the master’s thesis, with whom they prepare a draft thesis through consultations. In the fourth semester, the student prepares and defends their master’s thesis.
Explanation of the table: The table includes all obligatory courses specified upon enrolment in the stated academic year. Each listed course:
- serves as a link to the course syllabus,
- the letter L next to a course represents a link to the lecturer delivering the lectures for the selected course,
- the letter T next to a course represents a link to the lecturer conducting the tutorials for the selected course.
Obligatory Courses
| 1st year | 2nd year |
|---|---|
| Information Security Law - L, T | Secure Software Development - L, T |
| Network Security - L, T | Qualitative and Quantitative Research Methodology - L, T |
| Personal Cyber Security - L, T | Internet of Things and Operational Technologies Cyber Security - L, T |
| Data Security and Protection - L, T | Assessment and Audit of Cyber Security - L, T |
| Systems Security - L, T | Thesis Seminar - L, T |
| Organizations’ Security - L, T | Security of Web and Mobile Applications - L, T |
| Component Security - L, T | Master's Thesis |
| Cyber Security - L, T | |
| Elective Course 1 | |
| Elective Course 2 | |
| Elective Course 3 |
| 1st year | 2nd year |
|---|---|
| Information Security Law - L, T | Secure Software Development - L, T |
| Network Security - L, T | Qualitative and Quantitative Research Methodology - L, T |
| Personal Cyber Security - L, T | Internet of Things and Operational Technologies Cyber Security - L, T |
| Data Security and Protection - L, T | Assessment and Audit of Cyber Security - L, T |
| Systems Security - L, T | Thesis Seminar - L, T |
| Organizations’ Security - L, T | Security of Web and Mobile Applications - L, T |
| Component Security - L, T | Master's Thesis |
| Cyber Security - L, T | |
| Elective Course 1 | |
| Elective Course 2 | |
| Elective Course 3 |
| 1st year | 2nd year |
|---|---|
| Information Security Law | Secure Software Development |
| Personal Cybersecurity | Qualitative and Quantitative Research Methodology |
| Network Security | Internet of Things and Operational Technologies Cybersecurity |
| Data Security and Protection | Assessment and Audit of Cyber Security |
| Systems Security | Thesis Seminar |
| Organizations' Security | Security of Web and Mobile Applications |
| Component Security | Master’s Thesis |
| Cyber Security | |
| Elective Course 1 | |
| Elective Course 2 | |
| Elective Course 3 |
Elective Courses
- Corporate Security
- Global Security
- Security of Use of Intelligent Systems in Informatics
- Applied Cryptography
- Work Practice
- Data Mining (the course will be withdrawn as of the academic year 2025/2026)